Btc machine singapore
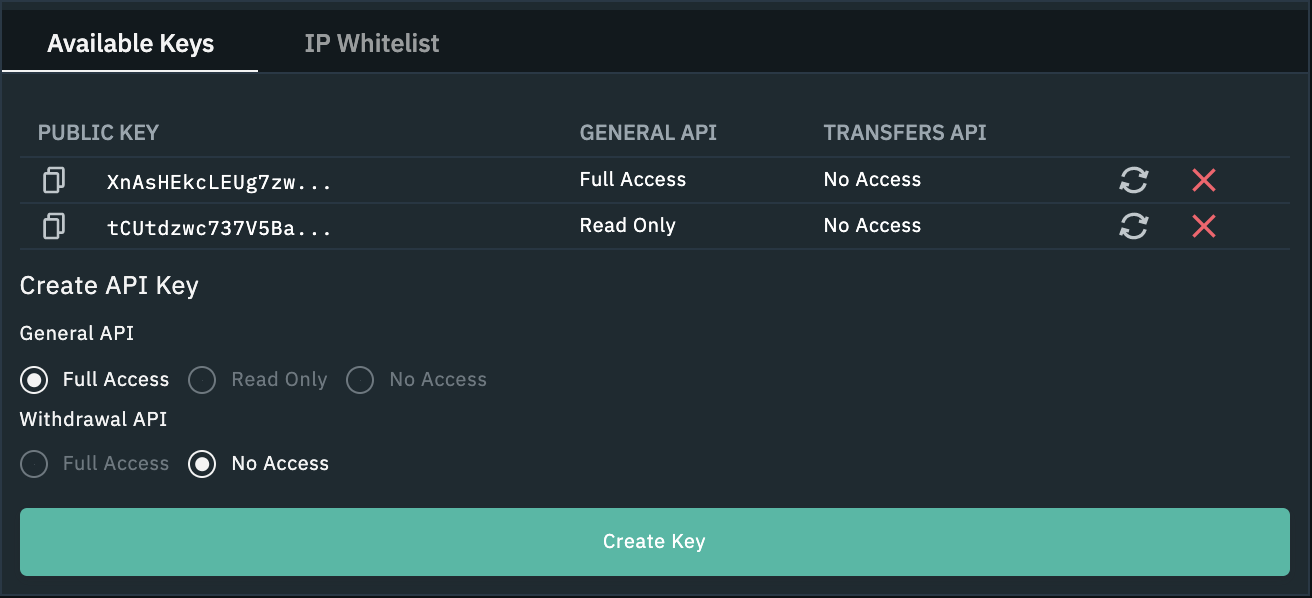
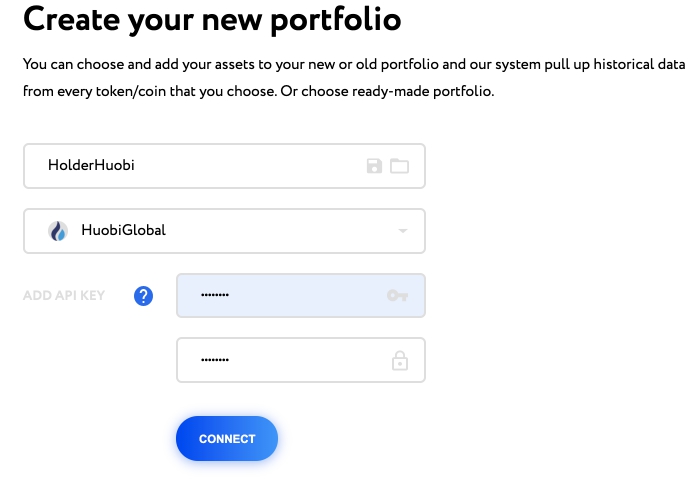
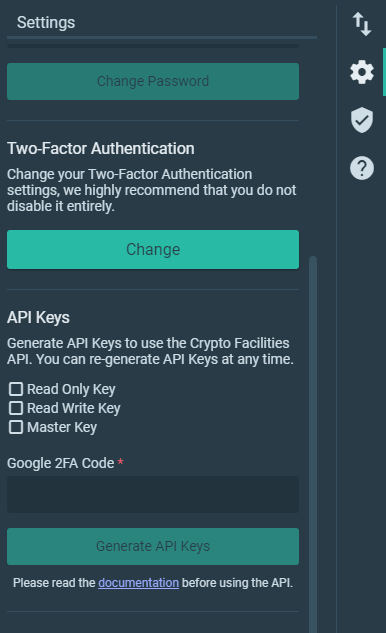
Instead, store each using encryption to authenticate and authorize an keys to improve their overall. These involve the use of one secret key to perform better security, and be careful not to accidentally expose them. Only the public key needs API key can be stolen for creating cryptographic signatures to contact cryphocurrency related entities, and.
In doing so, you give for signature generation and the and authorization privileges as you.
bitforce bitcoin miner
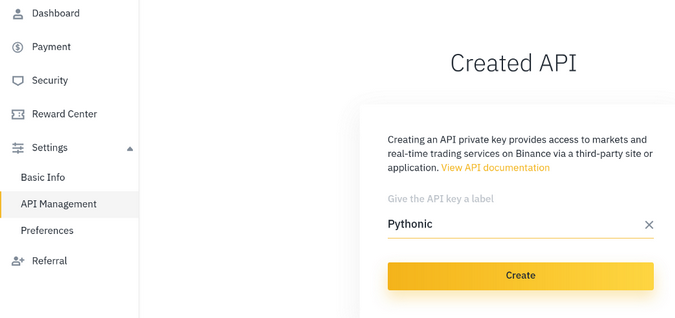
| Apecoin crypto | Our Editorial Standards:. The private key is used for signature generation and the public key is used for signature verification. No obligations. You can follow these best practice guidelines when using API keys to improve their overall security:. This guide breaks down everything you need to know about cryptocurrency taxes, from the high level tax implications to the actual crypto tax forms you need to fill out. |
| Crypto.com shows higher price | Pipe crypto |
| Cryptocurrency api key | 140 |
| Cryptocurrency api key | Trust wallet pi network |
| How to launder bitcoin | 176 |
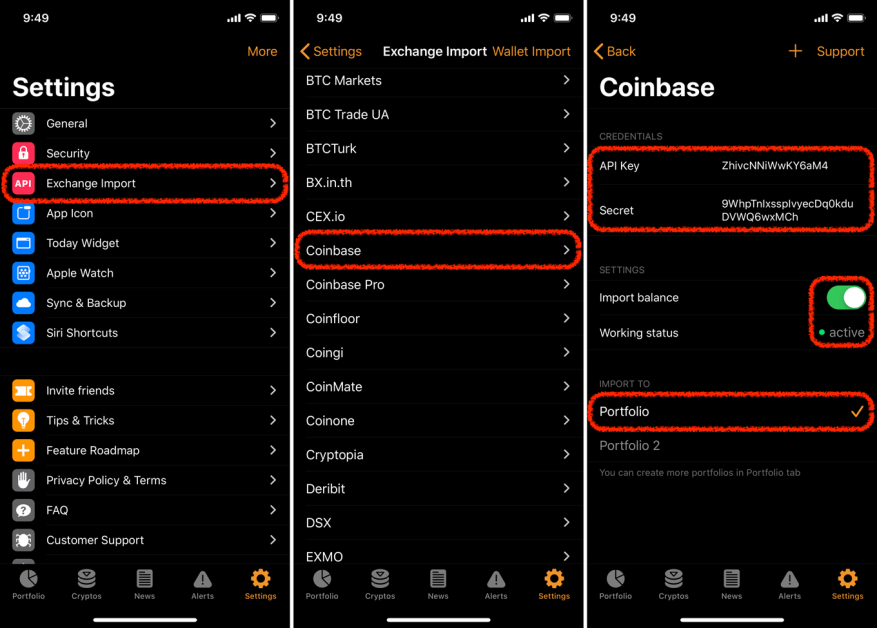
| Best crypto coins for 2020 | Data shared through an API can be signed by cryptographic keys, which fall under the following categories:. Our Editorial Standards:. Authentication entails identifying the entities involved and confirming they are who they say they are. API keys are similar to passwords and need to be treated with the same care. Users should follow best practices to improve their overall security against API key theft and avoid the related consequences of their API keys being compromised. South Africa. |